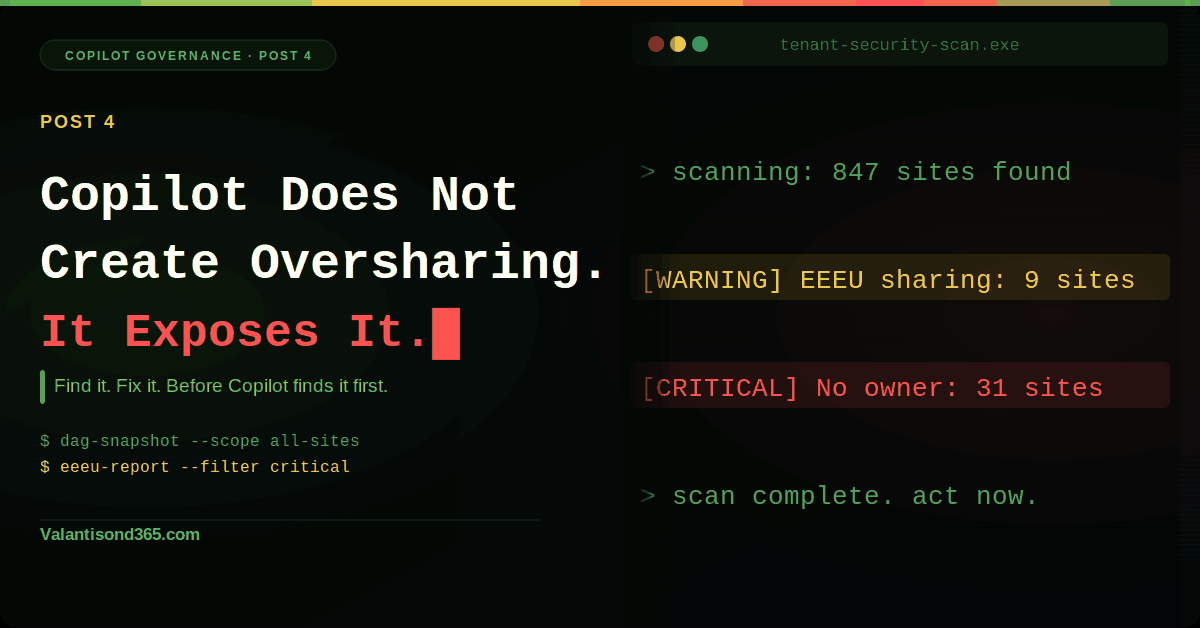
Post 4: Copilot Does Not Create Oversharing. It Exposes It
Use Data Access Governance reports to find your riskiest sites before you scale Copilot across the organisation. All steps and confirmed behaviours in this post verified against Microsoft Learn documentation, March 2026.
Why this post matters
Post 2 of this series covered the settings that stop new oversharing from happening: tightening org-wide sharing defaults, hiding EEEU from the People Picker, and blocking member resharing at site level. Those controls close the door on future exposure. They do not touch what was already shared before you ran them. That is what this post is for.
Copilot only returns content the user has permission to access. That sounds safe until you realise how much content is already over-permissioned in most tenants. Sites shared with Everyone except external users. Files with Anyone links. Thousands of users silently permissioned through broken inheritance. Copilot will surface all of it.
Before you extend Copilot access across the organisation, you need a prioritised list of the sites where oversharing is worst. Data Access Governance (DAG) reports give you that list. Two types of reports, two different lenses: snapshot reports show the current state of permissions across every site in the tenant, and activity reports show where active sharing is happening right now. This post walks through both, in the order Microsoft recommends running them.
Audience: SharePoint admins and Microsoft 365 consultants running Copilot readiness work for a client tenant.
Prerequisites
- SharePoint Administrator or Global Administrator role.
- SharePoint Advanced Management (SAM) licence. SAM is included with Microsoft 365 Copilot licences if at least one user in the tenant is assigned a Copilot licence, SharePoint admins automatically get access to all SAM features needed for Copilot deployment, including all DAG reports. Without a Copilot licence, SAM is available as a standalone Plan 1 add-on at $3 per user per month. Verify at Microsoft 365 admin centre > Billing > Licences. Source: Reference 7.
- For activity reports without a SAM licence: data collection must be enabled manually before running reports. After enabling, data is collected for 28 days and reports become available 24 hours later.
| Note on report availability. DAG reports are available in commercial, GCC, GCC-High, and DoD environments. They are currently unavailable for Gallatin tenants even with the required licences. Source: Reference 1. |
What you will have after this post
- A baseline snapshot of permissions across every SharePoint and OneDrive site in the tenant.
- A prioritised list of the top sites with the broadest user access, EEEU sharing, Anyone links, and guest permissions.
- Active oversharing identified from the last 28 days using activity reports.
- A filtered export ready to use for remediation planning, with high-risk lines of business flagged.
TL;DR
| Topic | The short version |
| Admin path | SharePoint admin centre > Reports > Data access governance |
| Snapshot report | Site permissions across your organisation. Runs across all SharePoint and OneDrive sites. First report takes up to 5 days. Subsequent reports within 24 hours. Data up to 48 hours old. Run quarterly. |
| Activity reports | Sharing links and EEEU reports. Cover SharePoint sites only (OneDrive via PowerShell). Top 100 sites per report. Data up to 24 hours old. Run monthly. |
| What each shows | Snapshot: total permissioned users, guest count, EEEU count, Anyone links, broken inheritance. Activity: sites with the most new sharing links or EEEU additions in the last 28 days. |
| Download limit | CSV export up to 1 million sites for both snapshot and activity reports. |
| SAM licence | Required for snapshot reports and remedial actions. Without SAM, activity reports limited to 10,000 sites and no remedial actions available. |
Step 1: Run the Site Permissions Snapshot Report
What this report tells you
The site permissions report is the starting point. It scans every SharePoint and OneDrive site in the tenant and produces a snapshot of the current permission state. You are not looking at recent activity here. You are looking at what exists right now, accumulated over the lifetime of the tenant.
Microsoft’s documentation is direct on why this matters for Copilot: since Copilot respects existing permissions, understanding your current permission structure is critical before deployment. Sites with many users accessing content pose the highest risk for unintended data exposure through Copilot interactions.
The report surfaces the following per site:
- Total permissioned users: all unique users who can access the site at any level, including through broken inheritance. Calculated by expanding all groups, removing duplicates, and counting the remainder.
- EEEU permission count: number of permissions where Everyone except external users is the recipient, at any scope.
- Anyone link count: number of existing Anyone links across all files in the site.
- People in your organisation link count: number of existing PeopleInYourOrg links.
- Guest user permissions: count of permissions to guests marked with #EXT# in their identity.
- External participant permissions: count of permissions to external users who sign in with their own credentials.
- Microsoft Entra group count: number of cloud-only groups with permissions at any scope.
- Items with unique permissions count: extent of broken inheritance across the site.
| Current vs potential exposure. Adding users directly increases the Total permissioned users count immediately. Creating sharing links or granting EEEU access does not increase the count until a user accesses content through those links. Both types of risk appear in the report but are counted differently. Source: Reference 2. |
Admin path
SharePoint admin centre > Reports > Data access governance > Site permissions across your organisation > View reports
Phase 1: Create the report
- Sign in to the SharePoint admin centre at https://admin.sharepoint.com.
- In the left navigation, expand Reports and select Data access governance.
- Under Site permissions across your organisation, select View reports.
- Select Create report to generate the first report. If a previous report exists, select Run reports to get the latest data. Note the button is only active once 30 days have passed since the last run.
- The system creates separate reports for SharePoint and OneDrive sites simultaneously.
| Confirmed as: documented behaviour. The first report takes up to 5 days regardless of organisation size. Subsequent reports complete within 24 hours. Data reflects permissions from up to 48 hours before generation. Reports can be re-run every 30 days. Source: Reference 2. |
Phase 2: Read the summary
Once the report is ready, select View report under the SharePoint or OneDrive section. The summary page shows:
- Total sites scanned.
- Sites without users: sites with no user permissions assigned.
- Sites with user permissions: broken down by SharePoint and OneDrive.
- Report date: when the data was captured, which may be up to 48 hours before generation.
The report displays the top 100 sites with the highest number of permissioned users. These are your highest-priority candidates for review. Sites at the top of this list are where a Copilot interaction is most likely to surface content a user did not expect to have access to.
Phase 3: Export and filter for high-risk lines of business
- Select Download report to export as CSV.
- The export contains data for up to 1 million sites.
- In the CSV, sort descending by Number of users having access to identify the broadest sites.
- Cross-reference Site Name and Primary admin email columns to identify HR, Legal, Finance, and M&A sites.
- Flag any site with EEEU permission count greater than 0 as high priority.
- Flag any site with Anyone link count greater than 0 for immediate review.
| Confirmed as: documented feature. CSV export available for up to 1 million sites. Columns include: Site Name, Site URL, Site Template, Primary admin, Primary admin email, Number of users having access, Guest user permissions, EEEU permission count, Anyone link count, People In Your Org link count, Items with unique permissions count, Site Sensitivity, External Sharing setting. Source: Reference 2. |
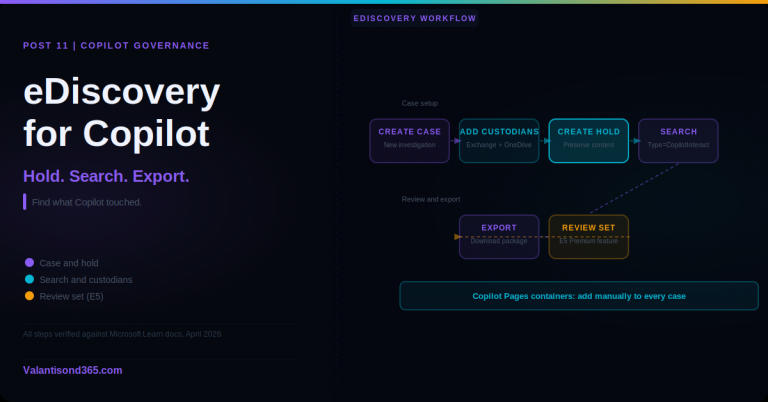
Step 2: Run the Activity Reports
What activity reports tell you
The snapshot report tells you what exists. Activity reports tell you what is actively happening. They cover the last 28 days and identify sites where users have been creating the most sharing links or adding EEEU permissions. These are the sites where oversharing is not historical. It is ongoing.
Two activity report types are available:
- Sharing links reports: identifies sites with the most new Anyone links, People in your organisation links, and Specific people links created in the last 28 days.
- EEEU activity reports: identifies sites where content was shared with Everyone except external users in the last 28 days, at either the site level or item level.
| SharePoint only in the admin centre. Activity reports in the SharePoint admin centre cover SharePoint sites only. OneDrive activity report data is available via PowerShell. Source: References 3 and 4. |
Admin path
SharePoint admin centre > Reports > Data access governance > Sharing links or Shared with Everyone except external users
Phase 1: Run sharing links reports
- From the Data access governance landing page, select the Sharing links section.
- Select individual reports to run, or run all at once:
- Anyone links: sites with the most Anyone links created in the last 28 days.
- People in the organisation links: sites with the most PeopleInYourOrg links created in the last 28 days.
- Specific people links shared externally: sites with the most externally targeted Specific people links created in the last 28 days.
- Check the Status column to confirm the report is ready. Reports may take up to 24 hours to complete.
- Once ready, select the report name to view the top 100 sites with the highest new link activity.
- Download as CSV for offline analysis. Export contains data for up to 1 million sites.
| Confirmed as: documented behaviour. Sharing links reports collect activity data from the last 28 days. The UI displays the top 100 sites by links created in the last 30 days (Microsoft docs use both figures: 28 days for the collection window, 30 days for the UI display). CSV export available for up to 1 million sites. Reports can be re-run every 24 hours. Source: Reference 3. |
Phase 2: Run EEEU activity reports
- From the Data access governance landing page, select the Shared with Everyone except external users section.
- Select Create report and configure:
- Report name: a unique name to identify this report.
- Template: choose specific site templates or select All sites.
- Privacy: for Team sites, filter by Private, Public, or All.
- Site sensitivity: optionally filter to specific sensitivity labels (for example, Confidential) to focus on high-risk sites.
- Report type: select Public sites (EEEU in site membership) or Public items (individual files or folders shared with EEEU).
- Run the report. It may take up to 24 hours to complete.
- Once ready, the report displays the top 100 sites with the highest EEEU sharing activity in the last 28 days.
- Download as CSV. The export contains up to 1 million sites sorted by EEEU sharing activity, highest first.
| Confirmed as: documented behaviour. EEEU reports cover SharePoint sites only in the admin centre. Maximum of 10 reports can be created. Data captured from up to 24 hours before generation. EEEU can occur via public sites (EEEU in site membership) or public items (individual files shared with EEEU). Source: Reference 4. |
Phase 3: Combine and prioritise
Run both report types and cross-reference the results. Sites that appear in both the snapshot report (high total permissioned users) and the activity reports (active link creation or EEEU sharing) are your highest-priority remediation targets.
Microsoft recommends this combination explicitly: run snapshot reports quarterly to maintain a baseline view, and run activity reports monthly to catch emerging risks.
For each high-risk site identified, note the Primary admin contact from the CSV. You will need these contacts for Site Access Reviews in Post 5. One thing to know before you get there: the admin centre UI lets you initiate reviews for up to 100 sites at a time. That is a UI limit, not a total cap. If your list has more than 100 sites, you work through them in batches using PowerShell, which has no such restriction. There is also a separate limit of 1,000 Site Access Reviews per calendar month from the site permissions report specifically. Source: Reference 5.
Validate
Check 1: Snapshot report completed and exported
- Confirm the site permissions report status shows as completed in the Data access governance landing page.
- Open the CSV export and confirm it contains columns for Site Name, Number of users having access, EEEU permission count, Anyone link count, and Primary admin email.
- Confirm at least one site appears with an EEEU permission count greater than 0 or an Anyone link count greater than 0. If none appear, the report may still be processing or the tenant has already cleaned up broad sharing.
| Expected result: A populated CSV with sites ranked by total permissioned users. High-risk lines of business (HR, Legal, Finance, M&A) identified by site name with primary admin contacts recorded. |
Check 2: Activity reports completed and prioritised
- Confirm at least one sharing links report and one EEEU report show status as completed.
- Open each report in the admin centre and confirm the top 100 sites list is populated.
- Cross-reference with the snapshot report CSV to identify sites appearing in both. Mark these as Priority 1 for remediation.
| Expected result: A combined list of high-risk sites with owner contacts, ranked by oversharing severity. This list is the input for Site Access Reviews in Post 5. |
Troubleshooting
| Symptom | Most likely cause | Fix |
| Report status shows Pending after 24 hours. | First-time snapshot report can take up to 5 days to complete, not 24 hours. | Wait up to 5 days for the first report. Subsequent reports complete within 24 hours. Source: Reference 2. |
| Activity report shows no data after enabling data collection. | Data collection requires 24 hours before the first report is available. Reports only contain data from the point collection was enabled. | Wait 24 hours after enabling data collection before running the first activity report. Source: Reference 1. |
| Activity reports not visible in the admin centre. | Without a SAM licence, data collection must be enabled manually before activity reports appear. | Go to Data access governance > Sharing links or EEEU section and enable data collection. Note: without SAM, activity reports are limited to 10,000 sites. |
| CSV export is empty or shows fewer sites than expected. | Report data reflects permissions from up to 48 hours before generation. Very recently created sites or permissions may not yet appear. | Wait 48 hours after permission changes before running the report to capture the current state accurately. Source: Reference 2. |
| Data collection paused automatically. | If no reports are generated for 3 months, data collection pauses automatically and must be re-enabled. | Re-enable data collection from the Data access governance landing page. Source: Reference 1. |
Lessons Learned
These come from working through DAG reports in real client tenants.
- Run the snapshot report first, before you touch anything else. The first run takes up to 5 days. Start it on day one of the engagement and let it run in the background while you complete Posts 1, 2, and 3. By the time you get to Post 4 steps, the report is ready.
- The top 100 in the admin centre UI is enough to identify the pattern. Download the full CSV for the detailed remediation list, but you can usually tell within the top 20 sites whether the tenant has a systemic oversharing problem or isolated cases.
- Total permissioned users is the number to sort by first. A site with 5,000 permissioned users through broken inheritance is a higher Copilot risk than a site with 10 Anyone links. Both need attention but sort by the bigger number first.
- EEEU and Anyone link counts in the snapshot reflect what exists. The activity reports show what is being actively created. A site with high existing EEEU count but no recent EEEU activity is a historical problem. A site with low existing count but high recent activity is a growing problem. Both go on the list but the active one gets addressed first.
- Use the Site sensitivity filter in EEEU reports to zero in on Confidential or Highly Confidential sites immediately. If those labels are deployed in the tenant, filtered EEEU reports on labelled content are the fastest way to find the highest-risk files.
- Collect the Primary admin email from every flagged site before leaving this step. Site Access Reviews in Post 5 require owner contacts. Do not skip this column in the export.
References
All links verified March 2026.
1. Data access governance reports for SharePoint and OneDrive sites – Overview of all DAG reports, licensing requirements, admin path, report types, and data collection requirements for tenants without SAM.
https://learn.microsoft.com/en-us/sharepoint/data-access-governance-reports
2. Get your organisation’s site permissions baseline with the snapshot report – Full documentation for the site permissions snapshot report. Covers report timing (5 days first run, 24 hours subsequent), data lag (up to 48 hours), CSV columns, and current vs potential exposure.
https://learn.microsoft.com/en-us/sharepoint/data-access-governance-site-permissions-report
3. Monitor sharing activities in SharePoint with sharing links activity reports – Documentation for the sharing links activity reports. Covers the three report types (Anyone, People in your organisation, Specific people), 28-day window, top 100 display, and CSV export.
https://learn.microsoft.com/en-us/sharepoint/data-access-governance-sharing-links-report
4. Monitor Everyone except external users (EEEU) sharing with the EEEU activity report – Documentation for the EEEU activity reports. Covers public sites vs public items, report configuration options including sensitivity label filtering, 28-day window, and CSV export.
5. Initiate site access reviews for Data access governance reports – Documents the Site Access Review remedial action available from DAG reports. Covers initiating reviews for up to 100 sites via the admin centre UI, and larger volumes via PowerShell.
https://learn.microsoft.com/en-us/sharepoint/site-access-review
6. Get ready for Microsoft 365 Copilot with SharePoint Advanced Management – Primary Copilot readiness source. Confirms that DAG reports are part of the recommended Copilot preparation workflow and explains the relationship between permissions and Copilot results.
https://learn.microsoft.com/en-us/sharepoint/get-ready-copilot-sharepoint-advanced-management
7. Licensing for SharePoint Advanced Management – Confirms which Copilot SKUs include SAM and the standalone SAM Plan 1 add-on option.
https://learn.microsoft.com/en-us/sharepoint/sharepoint-advanced-management-licensing
Conclusion
DAG reports give you the picture you need before you can act. Without knowing which sites are over-permissioned, any remediation effort is guesswork. With the snapshot report you have the baseline. With the activity reports you know where oversharing is growing.
The output of this post is a prioritised list of sites with owner contacts attached. That list is the direct input for Post 5, where Site Access Reviews, Restricted Access Control, and Restricted Content Discovery turn the findings into actual permission changes.
One thing worth saying to the clients at this point: the reports do not fix anything on their own. They surface the problem. The remediation happens in the next post. But you cannot make confident decisions about what to restrict or review without running these reports first.